
The Real CyberAttack simulation
based on Mitre Att&ck
HackMeUp is a professional Cyber Arena that combines realistic simulation, structured competition, and objective performance measurement.
Designed for students, cybersecurity professionals, and organizations that want to train in real operational environments.
This is not just practice.
It is performance validation.
TRAIN AGAINST REAL ADVERSARIES

50+ Threat Actor Groups
Train against a wide range of adversaries, from nation-state APTs to cybercrime organizations.
Real Campaigns, Not Fiction
Scenarios are based on real attack campaigns observed in the wild, not synthetic labs.
Adversary Tactics in Action
Experience real TTPs mapped to MITRE ATT&CK, from initial access to persistence and exfiltration.
Multi-Stage Intrusions
Follow the full attack lifecycle, just like in real incidents.
GLOBAL THREAT LANDSCAPE
CYBERCRIME ECOSYSTEM
FIN6 & FIN7
Wizard Spider
Conti / REvil / LockBit
Mantis (APT-C-23)
RUSSIA / EURASIA
APT28 (Fancy Bear)
APT29 (Cozy Bear)
Sandworm Team
Turla
CHINA / ASIA-PACIFIC
APT41 (Double Dragon)
APT10 (MenuPass)
APT3 (Gothic Panda)
APT17 / APT18
NORTH KOREA / MIDDLE EAST
Lazarus Group (Corea del Nord)
AppleJeus
OilRig (APT34 - Iran)
Agrius / Ajax Security Team
Thanks to HackMeUP you can train on

Digital Forensic
Structured analysis of compromised systems aimed at collecting, preserving, and interpreting digital evidence.

Email Threat Investigation Investigation of email-based threats such as phishing, spear phishing, and business email compromise (BEC).

Network Threat Hunting Proactive identification of threats within network traffic.

Malware Analysis
In-depth examination of malicious code to understand its behavior, evasion techniques, and system impact.

Attack Simulation
Realistic simulation of cyber attacks to assess an organization’s security posture.

APT Threat Scenarios Simulation of advanced persistent threat campaigns involving sophisticated adversaries.

Security Operation Centre Exercises
Operational exercises that replicate a real SOC environment.
Threat Intelligence
Collection, analysis, and contextualization of threat data to support informed security decisions.
5 DIFFICULTY LEVELS - FROM BEGINNERS TO APT-LEVEL
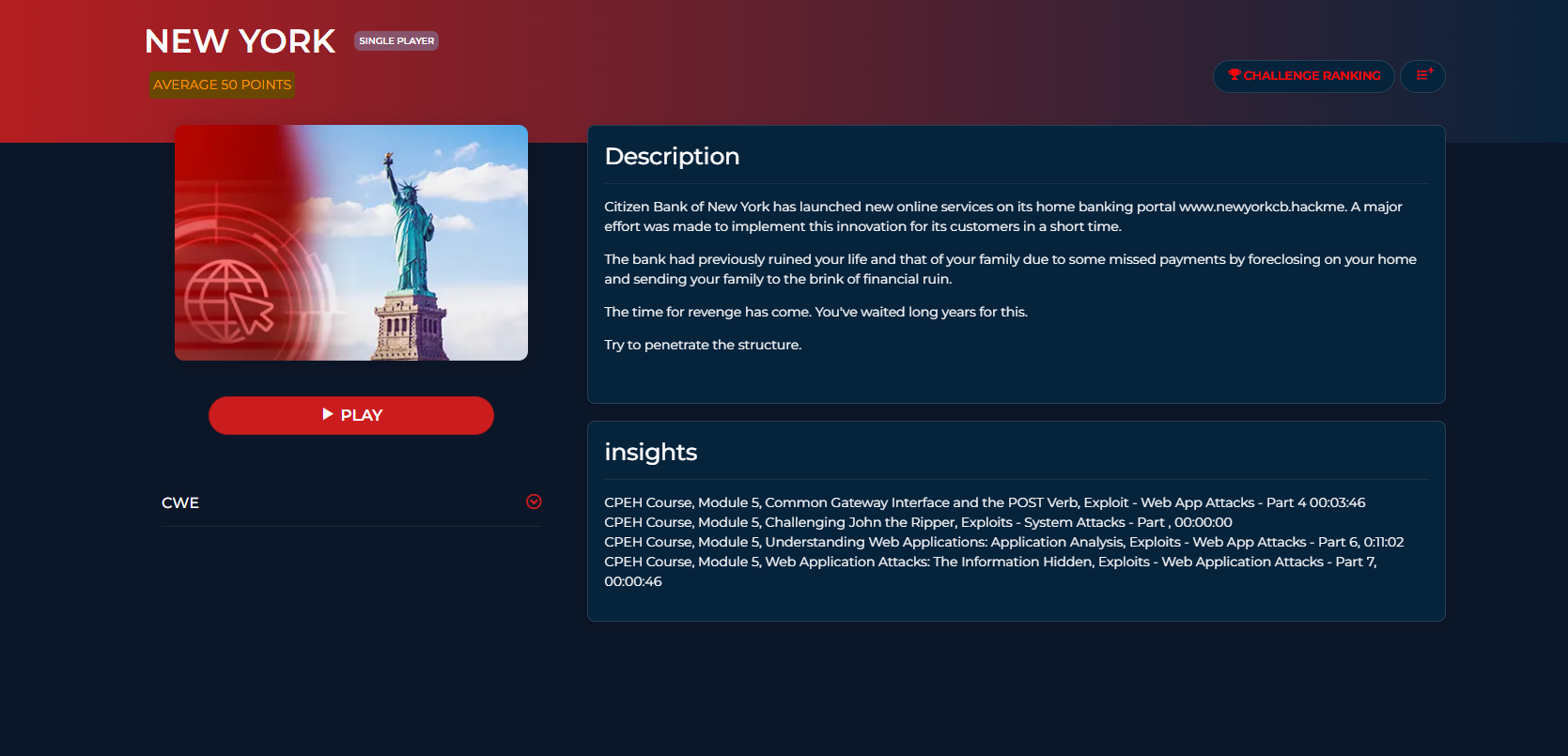
200+ SCENARIOS • FULL MITRE ATT&CK MAPPING

Offensive Security Operations
Dive into realistic attack simulations. Master exploitation, privilege escalation, and lateral movement across complex infrastructures from Detroit to Tokyo.

Blue Team & SOC Dynamics
Train in high-pressure environments. Learn to monitor and mitigate live attacks in professional SOC workflows, featuring scenarios in Johannesburg, Viterbo, and Lyon.

Global APT Emulation
HackMeUp integrates the power to simulate the Tactic, Techniques, and Procedures (TTPs) of over 50 world-class threat actors mapped to the MITRE ATT&CK® framework.

Custom Kill Chain
Take total control of your training experience with our unique Dynamic Configuration engine.
REALISTIC ATTACK AND DEFENCE SIMULATIONS
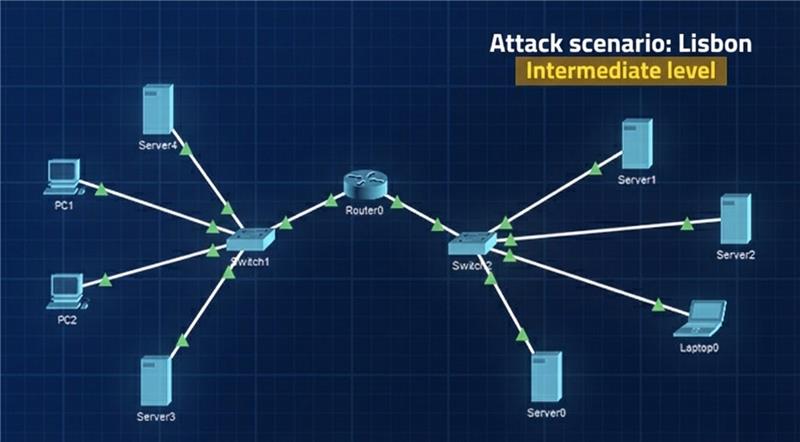
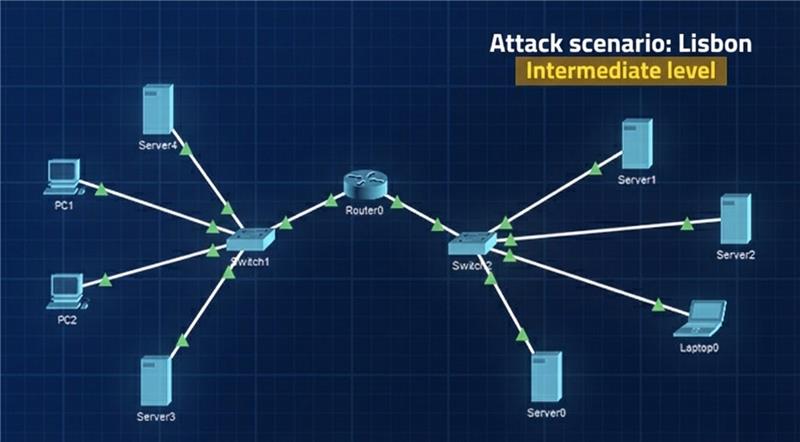
The challenges are designed for both Blue Team and Red Team training. Each challenge presents a realistic scenario.
Blue challenges focus on incidents and threats affecting the systems in the scenario.
Red challenges take place in a simulation of a complex infrastructure, with attack opportunities that are exactly those commonly found in such environments.

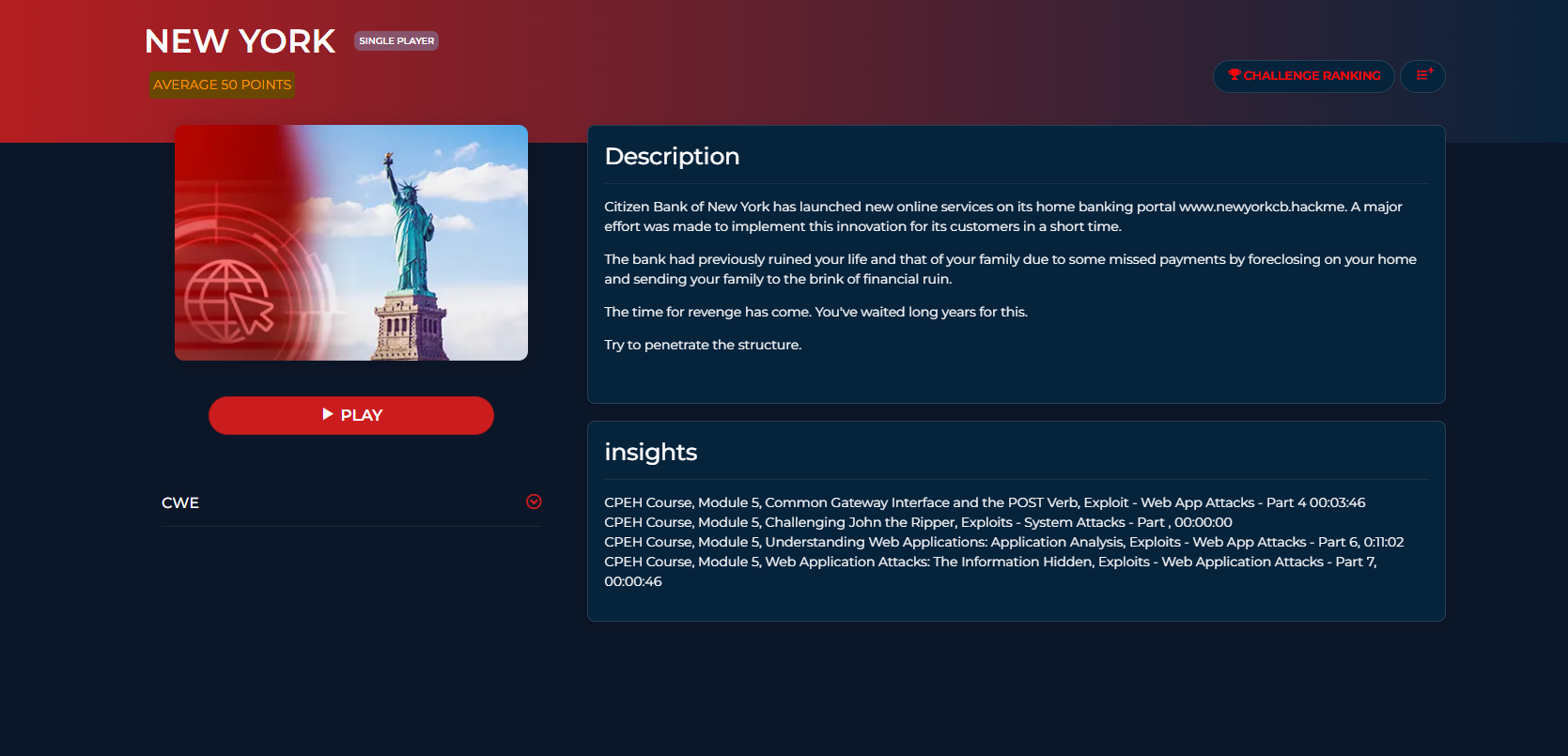
MAPPING CHALLENGES WITH MITRE ATT&CK® TECHNIQUES
Adversarial Tactics, Techniques, and Common Knowledge (or MITRE ATT&CK) is a classification system that describes cyber attacks: all our challenges have been classified using this system, so you can train yourself on specific attack techniques by searching through the MITRE ATT&CK categories.
TRACKING INDIVIDUAL IMPROVEMENT
The challenges are primarily intended as individual training. Participation in each challenge is evaluated based on a series of metrics, both temporal and merit-based, so that each participant can use them to track their technical progress. The metrics are tracked over time and weighted in various ways, so that everyone can have a clear picture of their progress in defence or attack capabilities.


VARIABLE COMPLEXITY OF SCENARIOS BASED ON SKILLS ACHIEVED
Indication of the skills required for each workshop
The different challenges will therefore be classified according to difficulty as well as the techniques to be used: this implies the need for skills for each participant who wants to take on the challenges. No one will be able to mistakenly take on a challenge that is beyond their capabilities, as the skill requirements will be clear.
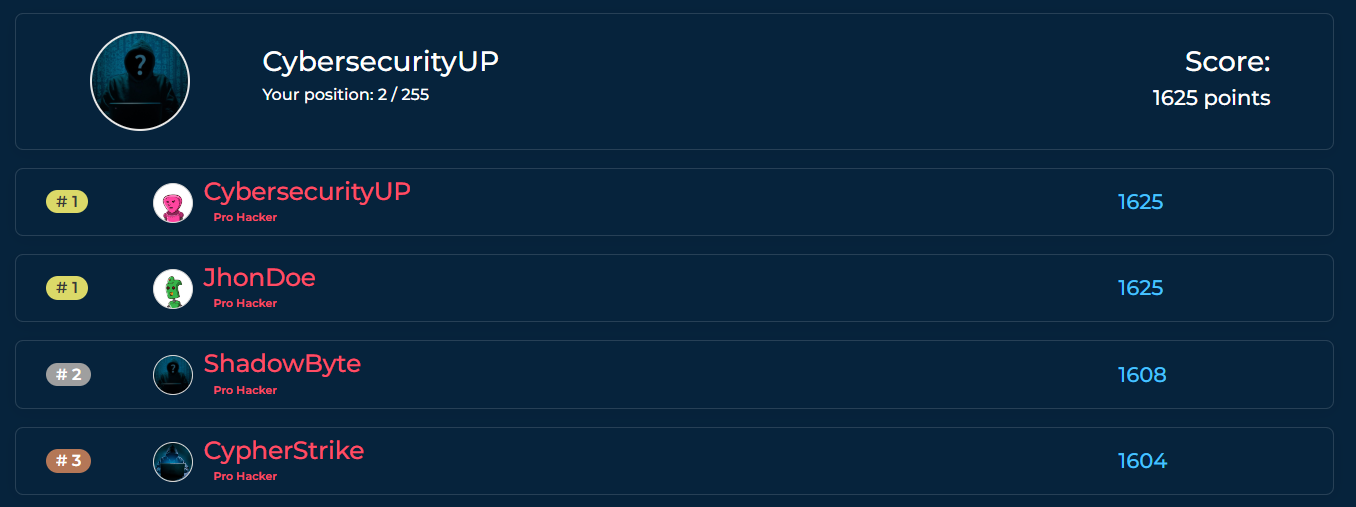
GLOBAL SCOREBOARD TO COMPETE WITH OTHER HACKERS
Individual assessment metrics may be compared with other hackers or defenders who take on our challenges. This constant benchmarking will be a strong incentive for personal improvement. The comparison will naturally be assessed at equal levels of difficulty, but also in absolute terms when participants have taken on many challenges of varying difficulty.
Gamification
Our platform will enable different forms of games among members. Competition, fun and challenges within challenges will be further motivation for growth for everyone, but especially for working groups (Red or Blue) who, together or against each other, will have to face the real world.


Final lesson on solving laboratory problems held by CybersecurityUP lecturers
REALISTIC ATTACK AND DEFENCE SIMULATIONS
The challenges are designed for both Blue Team and Red Team training. Each challenge presents a realistic scenario.
Blue challenges focus on incidents and threats affecting the systems in the scenario.
Red challenges take place in a simulation of a complex infrastructure, with attack opportunities that are exactly those commonly found in such environments.
MAPPING CHALLENGES WITH MITRE ATT&CK® TECHNIQUES
Adversarial Tactics, Techniques, and Common Knowledge (or MITRE ATT&CK) is a classification system that describes cyber attacks: all our challenges have been classified using this system, so you can train yourself on specific attack techniques by searching through the MITRE ATT&CK categories.

TRACKING INDIVIDUAL IMPROVEMENT
The challenges are primarily intended as individual training. Participation in each challenge is evaluated based on a series of metrics, both temporal and merit-based, so that each participant can use them to track their technical progress. The metrics are tracked over time and weighted in various ways, so that everyone can have a clear picture of their progress in defence or attack capabilities.

VARIABLE COMPLEXITY OF SCENARIOS BASED ON SKILLS ACHIEVED

Indication of the skills required for each workshop
The different challenges will therefore be classified according to difficulty as well as the techniques to be used: this implies the need for skills for each participant who wants to take on the challenges. No one will be able to mistakenly take on a challenge that is beyond their capabilities, as the skill requirements will be clear.
GLOBAL SCOREBOARD TO COMPETE WITH OTHER HACKERS
Individual assessment metrics may be compared with other hackers or defenders who take on our challenges. This constant comparison will be a strong incentive for personal improvement. The comparison will naturally be assessed at equal levels of difficulty, but also in absolute terms when participants have taken on many challenges of varying difficulty.
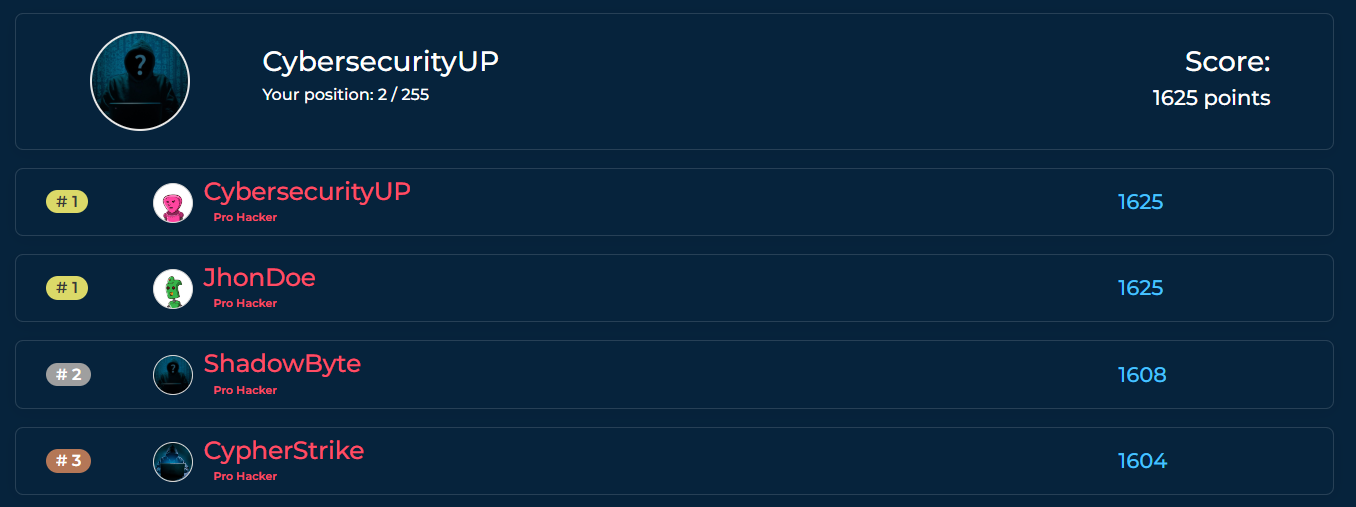
Gamification
Our platform will enable different forms of play among members. Competition, fun and challenges within challenges will be further incentives for growth for everyone, but especially for working groups (Red or Blue) who, together or against each other, will have to face the real world.

Final lesson on solving laboratory problems held by CybersecurityUP lecturers

Why are we different from other platforms?
Because we have devised challenges that take place solely and exclusively in complex environments, therefore in one or more networks and with a variable number of targets (machines and services) that are never singular.
Because you will find specific lessons on how to solve the scenarios. But be careful ! If you look at the solution before you have solved the scenario, you will pay a price in terms of your ranking in the competitions you are participating in.
We will also provide learning references: for each challenge, we will list the required skills and point to the specific module (or section) of our courses where participants can build or strengthen the knowledge needed to solve it.


